
Colonial Pipeline’s facility in Linden, New Jersey.Debra L. Rothenberg/Zuma
On Saturday, Colonial Pipeline, a company that runs large fuel storage and transfer facilities, announced it was the victim of a ransomware attack. In such attacks, hackers seed victim computers with malicious software to steal or encrypt files. Then, true to the name, the hackers hold the information ransom, threatening to either destroy or publicly release the files if the victim refuses payment. Over the past year, such high-profile attacks have become more common, with the Colonial Pipeline incident spotlighting the risk from ransomware gangs to highly visible and critical infrastructure.
The hack drew a swift response from the White House and senior national security officials. While the ransomware scene is dominated by Russian-speaking gangs that, according to an April announcement from the US Treasury Department, can work alongside or at least with the tacit approval of the Russian government, speaking to reporters on Monday, President Joe Biden said there was so far nothing to indicate the pipeline ransomware was a Russian government cyber attack. He did suggest there was evidence the perpetrator or their software was “in Russia. They have some responsibility to deal with this.”
At least 2,354 US-based government, healthcare, and educational institutions faced some level of ransomware attack in 2020, according to a recent analysis by Emsisoft, a cybersecurity company. The actual number is almost certainly higher, Emsisoft says, since some companies don’t disclose that they’ve been hit. It is also unknown how much ransom has been paid to attackers; Emsisoft estimates put the global floor at more than $18.6 billion in 2020, with more than $920 million of that coming from victims in the US.
The Colonial Pipeline attack is just the latest high-profile ransomware situation to become public. In late April the Washington, D.C., Metropolitan Police Department admitted it had been hacked. It soon became clear that the department had been the victim of one kind of ransomware attack after a Russian-speaking criminal group posted screenshots of what appeared to be sensitive internal police files. The hackers, who used a relatively new strain of malicious software known as “Babuk,” claimed they’d stolen more than 250 gigabytes of the deparment’s data, ranging from job applicants’ information to the names of confidential informants. Unless the cops paid up, they threatened to give some of what they had obtained to local gangs—a claim that seemed designed to get attention.
Within days of that attack coming to light, the group already was singing a different tune. The hackers pulled down what they had made available, as someone claiming to be from the group told a Polish news site that they were done with such attacks and did not want to be associated with “Russian ‘state’ hackers” or “cause a conflict between the Russian Federation and the United States.” But they weren’t getting out of the business; they promised to make the software they’d used freely available. A subsequent message on their website announced plans to continue stealing data and extorting organizations. This week, the group seemed to reverse themselves, and again threatened to release the DC department’s data unless they were paid.
According to an April New York Times article, DC was one of several police departments in the US to be hit by hackers in as many weeks. One Florida department had internal police contracts, jail surveillance videos, and what appear to be crime scene and victim photos posted online, where they are still accessible. A police department in Maine also currently has some of its data posted online, including unredacted witness statements, photos, and other sensitive material.
The Illinois Attorney General’s office suffered another high-profile—and ongoing—attack that it says was first discovered on April 10. The group behind the hack claims to have roughly 200 gigabytes of “confidential” data, including case file notes and information on state prisoners. The files remain available on the group’s website.
Allan Liska, an intelligence analyst and malware expert at the cybersecurity firm Recorded Future, tweeted that the DC hackers’ threat to expose confidential informants “serves as a nice reminder of what worthless bastards ransomware actors are. No amount of Bitcoin is worth putting someone’s life at risk.”
Liska told Mother Jones that although there is some mild disagreement in the cybersecurity community about exactly how the ransomware problem is getting worse—whether there are more one-off minor ransoms, for instance, or more attacks on higher-profile targets—there is wide consensus that it is growing, and that payments to perpetrators are on the rise.
“The extortion ecosystem has gotten a lot worse,” Liska says. “Ransomware actors have gotten more bold, and they’re finding new and more evil, inventive, ways to extort payment for those victims that won’t pay just to decrypt their files.”
Brent Callow, a ransomware expert at Emsisoft, says both the number of high-profile victims and attackers’ willingness to go to extreme lengths to extort their victims have grown. Beside the threat to DC’s police informants, he cites another case where the perpetrators said they found pornography on the computer of the victim company’s IT director. “They blamed his distraction for the fact that their attack succeeded (‘God bless his hairy palms,’ they wrote),” Callow said in an email. The company quietly paid up, he says, likely hoping to avoid a potential lawsuit if customers came to believe their data was compromised.
Attacks based on threats to leak data aregrowing more common, according to Emsisof. At the beginning of 2020, the company says, just one group was stealing data and threatening to release it in order to extort payment; by the end of the year, at least 17 other groups had adopted the practice and were publishing material on leak websites.
That some prominent attacks have links to Russia and potentially to Russian state-sponsored hacking outfits adds national security and geopolitical wrinkles to an already difficult law enforcement challenge. “It’s not just the comingling of resources, but in some cases we think it might be the commingling of people,” Liska says. “So, I work for the Russian government Monday, Wednesday, Friday. Tuesday, Thursday—I conduct my ransomware operations. That makes it very hard for law enforcement go after the main actors.”
Treasury’s April release on the ransomware groups was part of a broader Biden administration response to the Russian government hack of SolarWinds, a private US government contractor, that led to nine US federal agencies and more than 100 private companies being infiltrated in a more traditional act of espionage. In a March speech laying out his cybersecurity priorities, Department of Homeland Security Sec. Alejandro Mayorkas called ransomware “a national security threat,” while taking a delicately-worded veiled swipe at the Russian government by saying they do “not use the full extent of their authority to stop the culprits.”
The FBI on Monday attributed the Colonial attack to the DarkSide ransomware variant, a tool that is programmed to avoid systems operating in Russian or other languages used in former Soviet territories and that allows affiliate groups to split ransoms with the software’s original developers. Anne Neuberger, the deputy national security adviser for cybersecurity at the National Security Council, said on Monday that the pipeline hack was being viewed as a criminal matter, but questions about connections to nation-state actors are “certainly something that our intelligence community is looking into.”
A message posted by the attackers claimed they “do not participate in geopolitics.” “Our goal is to make money,” they wrote, discouraging speculation that would “tie us with a defined government and look for other…motives.”
Indeed, Emisoft’s Callow told Mother Jones that there is so far no indication to suggest anything at work beside greed. But he cautioned that “the groups may not even realize who their affiliates and partners really are.”
“What better to camouflage an act of cyberterrorism than to proxy it through a known for-profit criminal enterprise,” Callow asks.
A recent report from a ransomware task force of government, academic, and private sector representatives called for strengthened international coordination to attack the problem, and proposed broad solutions such as discouraging ransom payments, increasing pressure on countries that play host to ransomware groups, and more coordination on legal and investigative measures to block them.
Callow said that small to medium-sized businesses suffer most of the attacks, but because of the incidents’ small size and the fact they are often kept quiet, they don’t always make headlines. Indeed, the same group that is currently hosting sensitive data from the Florida police department has dozens of other organizations’ data posted on a site it maintains on the dark web, including a small office supply vendor on the Atlantic coast, a chiropractor in the US southwest, and a sign vendor in Canada.
Liska agrees the problem is larger and more common than small business owners realize, saying that most of them assume hackers focus on bigger, more splashy, companies.
“Organizations will read what you write and say, ‘That’s terrible, that’s awful, but I don’t have to worry about it because I’m not going to be targeted by Russian cyber criminals,’” he says. While some industries do face greater risks, he warns that “this is a broad swath of targets that they’re going after. They’ll hit whoever they can hit in order to get their money.”
This article has been updated with new information about the attack on DC police.



More Stories
Best Carry-On Luggage: Your Ultimate Travel Companion
How the P10 Mask Enhances Your CPAP Experience
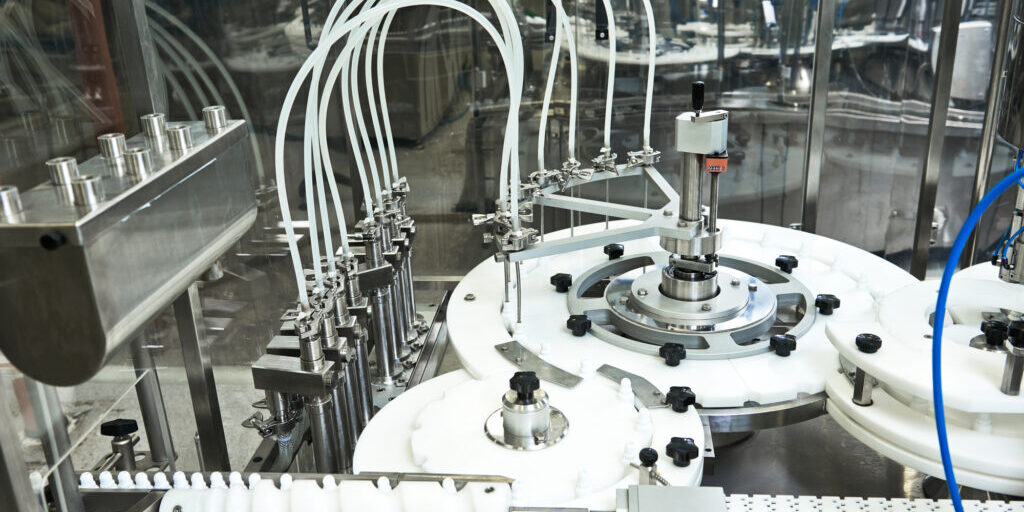
Evaluating the Efficiency of Different Liquid Filling Machine Manufacturers